Technofist
Image Processing Projects and training for Engineering Students in Bangalore, Image Processing cse projects 2018-2019
At TECHNOFIST we provide academic projects based on Image processing with latest IEEE papers implementation. Below mentioned are the 2018 list and abstracts on Image processing domain. For synopsis and IEEE papers please visit our head office and get registered.
OUR COMPANY VALUES
Instead of Quality, commitment and success.
OUR CUSTOMERS
Our customers are delighted with the business benefits of the Technofist software solutions.
IEEE 2018-2019 IMAGE PROCESSING BASED PROJECTS
Image processing is processing of images using mathematical operations by using any form of signal processing for which the input is an image, a series of images, or videos etc. Here we provided a variety of IEEE 2018-2019 Image processing list with abstract.
We provide real time latest IEEE Image processing projects for computer science and information science engineering students with Good Explanation and training and implementation. Latest 2018 and 2019 IEEE papers are available for final year engineering students to choose from.

IMAGE – PROCESSING PROJECT ABSTRACT
| ID | ABSTRACT |
|---|---|
| TIPO01 | ONE-TIME PASSWORD FOR BIOMETRIC SYSTEMS: DISPOSABLE FEATURE TEMPLATES – Biometric access control systems are becoming more commonplace in society. However, these systems are susceptible to replay attacks. During a replay attack, an attacker can capture packets of data that represents an individual’s biometric. The attacker can then replay the data and gain unauthorized access into the system. Contact: +91-9008001602 080-40969981 |
| TIP002 | ENHANCED PASSWORD PROCESSING SCHEME BASED ON VISUAL CRYPTOGRAPHY AND OCR – Traditional password conversion scheme for user authentication is to transform the passwords into hash values. These hash-based password schemes are comparatively simple and fast because those are based on text and famed cryptography. However, those can be exposed to cyber-attacks utilizing password by cracking tool or hash-cracking online sites. Contact: +91-9008001602 080-40969981 |
| TIPO03 | FULLY INCREMENTING VISUAL CRYPTOGRAPHY FROM A SUCCINCT NON-MONOTONIC STRUCTURE – Visual cryptography (VC) is a variant form of secret sharing. In general threshold setting, the k-out-of-n VC allows that, in a set of n participants, any k can recover and reconstruct the secret by stacking their shares. Contact: +91-9008001602 080-40969981 |
| TIPO04 | ILLUSIONPIN: SHOULDER-SURFING RESISTANT AUTHENTICATION USING HYBRID IMAGES – We address the problem of shoulder-surfing attacks on authentication schemes by proposing IllusionPIN (IPIN), a PIN-based authentication method that operates on touchscreen devices. Contact: +91-9008001602 080-40969981 |
| TIP005 | REVERSIBLE DATA HIDING IN ENCRYPTED IMAGES USING INTERPOLATION-BASED DISTRIBUTED SPACE RESERVATION – Reversible data hiding (RDH) in encrypted images has attained more attention recently in research community. Contact: +91-9008001602 080-40969981 |
| TIP006 | PASSNEIGHBOR:A SHOULDER SURFING RESISTANT SCHEME – We address the problem of shoulder-surfing attacks on authentication schemes by proposing IllusionPIN (IPIN), a PIN-based authentication method that operates on touchscreen devices. Contact: +91-9008001602 080-40969981 |
| TIP007 | ACCURATE DETECTION AND RECOGNITION OF DIRTY VEHICLE PLATE NUMBERS FOR HIGH-SPEED APPLICATIONS – This paper presents an online highly accurate system for automatic number plate recognition (ANPR) that can be used as a basis for many real-world ITS applications. Contact: +91-9008001602 080-40969981 |
| TIPO08 | SEMI-SUPERVISED IMAGE-TO-VIDEO ADAPTATION FOR VIDEO ACTION RECOGNITION – Human action recognition has been well explored in applications of computer vision. Contact: +91-9008001602 080-40969981 |
CONTACT US
For IEEE paper and full ABSTRACT
Phone: +91 9008001602
Email: [email protected]
Technofist provides latest IEEE 2018 — 2019 Image processing Projects for final year engineering students in Bangalore | India. Image processing Based Projects with latest concepts are available for final year ece / eee / cse / ise / telecom students.
ABOUT IMAGE PROCESSING
Image processing is processing images using mathematical operations by using any form of signal processing, for which the input is an image, a series of images, such as a photograph, the output of image processing may be either an image or a set of characteristics or parameters related to the image.
Most image-processing techniques involve isolating the individual color planes of an image and treating them as two-dimensional signals and applying standard signal-processing techniques to them. Images are also processed as three-dimensional signals with the third dimension being time or the z-axis.
Image processing usually refers to digital image processing, but optical and analog image processing also are possible. This article is about general techniques that apply to all of them. The acquisition of images (producing the input image in the first place) is referred to as imaging.
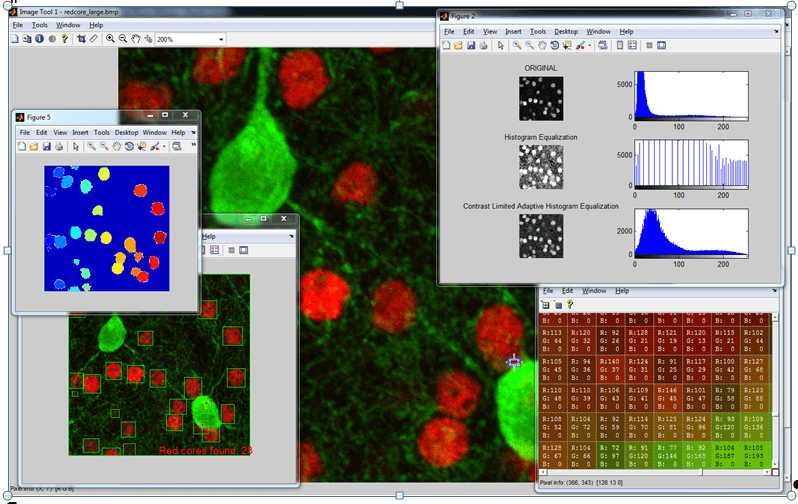

Technics Used in IMAGE PROCESSING Projects
- Image Acquisition
- Preprocessing
- Enhancement
- Analysis
- Reconstruction
- Compression
Image Acquisition
Image acquisition or Digital imaging is the creation of photographic images, such as of a physical scene or of the interior structure of an object.
Modern Technologies used for Image Processing
- Image sharpen & reinstatement:
Image sharpens & reinstatement is the procedure of images which is captured by the contemporary camera making them an improved picture or manipulating the pictures in the way to get chosen product. -
Facial Recognition:
Face recognition is a PC innovation that decides the positions and sizes of human faces in self-assertive digital pictures. -
Remote detection:
Remote detecting is little or substantial scale procurement of data of article or incident, with the utilization of recording or ongoing detecting apparatus. -
Pattern detection:
The pattern detection is the study or investigation from picture processing. -
Color processing:
The color processing comprises processing of colored pictures and diverse color locations which are utilized.
###
